Cybersecurity plays a pivotal role in the growth of the information society. At the same time, it remains a core research area in computer science. Therefore, its importance has become increasingly clear. In particular, growing media attention highlights today’s cybersecurity challenges.
To begin with, cybersecurity is a broad field. For example, it includes cryptography, software security, data privacy, system security, and network security. Therefore, this specialisation focuses on deep technical and theoretical expertise. Moreover, it builds on strong research in cryptography, programming languages, and semantics. In addition, students gain knowledge of key techniques. For instance, this includes classic tools such as encryption and digital signatures. However, it also covers advanced protocols. In particular, these include secure multiparty computation and zero-knowledge proofs. Furthermore, cybersecurity requires understanding system security and cryptographic engineering. For example, this involves protection against side-channel and fault attacks. Similarly, it includes secure software development. As a result, students learn to prevent bugs and malware through program analysis and verification.
For example, major data breaches such as the Equifax hack exposed millions of records. Likewise, the WannaCry attack disrupted hospitals and businesses worldwide. Closer to home, Mærsk and Demant were also affected. As a result, they suffered losses of 2.5 billion DKK. Although the financial impact is high, the broader implications are even more serious. Indeed, these incidents highlight the need for secure systems. Therefore, how can we protect data and build trust? Ultimately, cybersecurity addresses these challenges. Consequently, it is one of the most important and fast-growing fields in computer science today.
After you graduate:
PhD studies: After the first year of the MSc programme, you can apply for admission to the department's PhD programme in computer science. All positions are fully-funded.
Industry: Huge demand for CS graduates in the Aarhus region. There are many software companies or general companies with large IT departments in Aarhus and in Denmark, e.g. Cryptomathic, Partisia, Sepior, Concordium, Chainalysis, etc.
Please note that details regarding general programme structures and brief study plans are subject to change and are not legally binding. Only the official regulations and study plans are authoritative.
These courses are designed to equip students with the essential skills and knowledge required for success in the cybersecurity field.
FALL | SPRING |
| Advanced Topics in Cybersecurity (10 ECTS) | Cryptologic Protocol Theory* (10 ECTS) |
| Cryptographic Computing * (10 ECTS) | Systems Security (10 ECTS) |
| Cryptology* (10 ECTS) | Language-based Security (10 ECTS) |
| Formal Software Verification (10 ECTS) | |
| Program Analysis (10 ECTS) | |
| Quantum Information Processing (10 ECTS) | |
| Succinct Proof Systems (10 ECTS)** |
(*) Cryptology is prerequisite for Cryptologic Protocol Theory and Cryptographic Computing
(**) Offered from 2026
Ready to deepen your knowledge? Our supplementary courses offer students the opportunity to broaden their expertise in related fields.
Students may also select elective courses from computer science department or from other departments, provided they are relevant to their area of specialisation.
FALL | SPRING |
| Program Logics (10 ECTS) | Algorithmic Model Checking (10 ECTS) |
| Advanced Topics in Programming Language Theory (10 ECTS) | |
| Indledende Algebra 1+2 (5 +5 ECTS)*** |
(***) Only offered in Danish
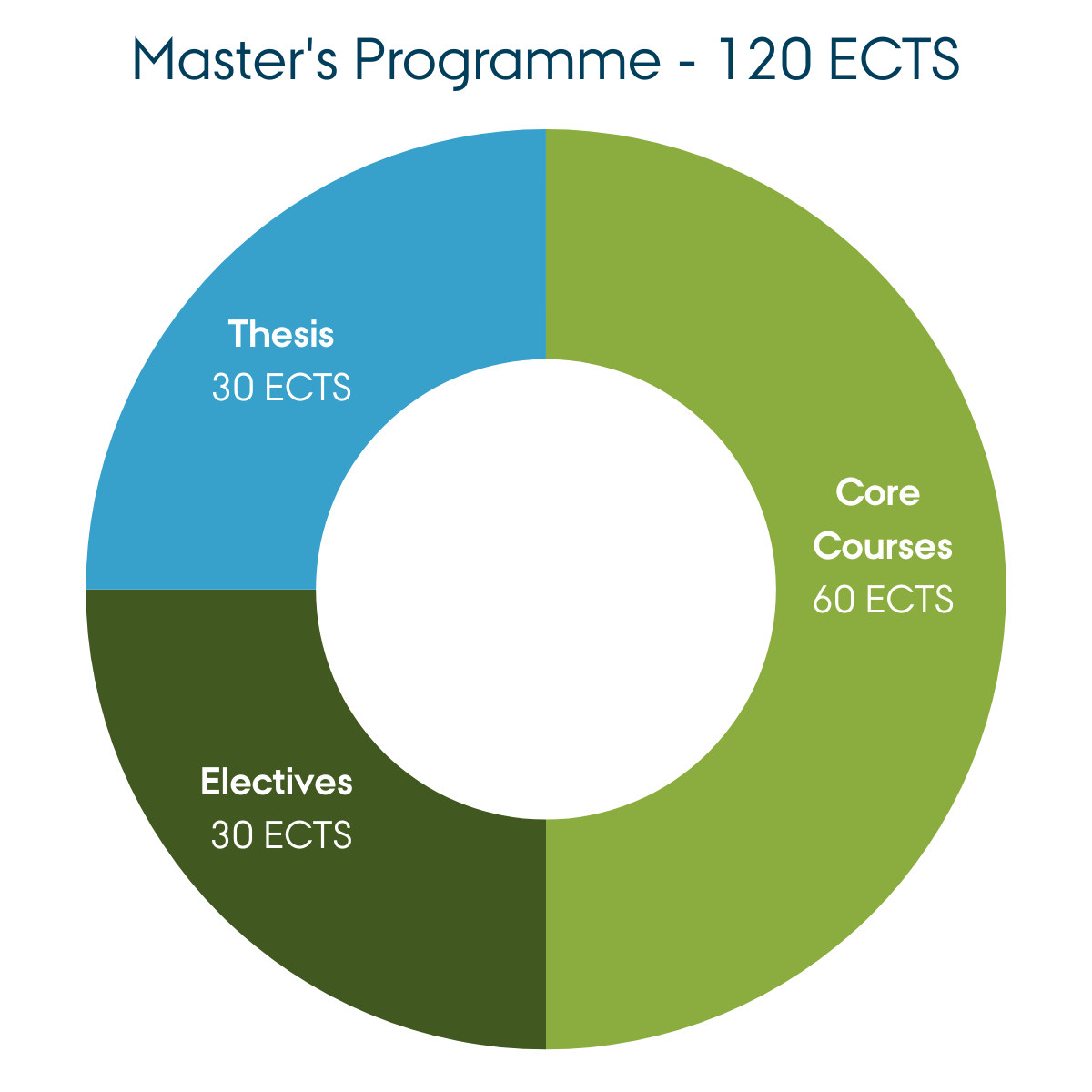
Learn more about the programme structure and the courses offered within the specialisations and course packages.
See more details about the master's degree programme in Danish or English.